OpenAI introduced a new cybersecurity initiative, Daybreak, on May 11, designed to find, validate, and help fix software vulnerabilities before attackers can exploit them.
The firm describes the approach as making software “resilient by design,” moving security earlier into the build cycle through AI-assisted code review, threat modeling, patch validation, and dependency analysis.
For crypto, where a software failure can result in an immediate capital loss within a single block, the urgency is clear.
The standard pattern in the crypto industry is reactive, going through a pre-launch audit, post-deployment monitoring, response when funds move, a post-mortem on the method, vulnerability patching, reimbursement negotiation, and governance debate.
That model has the weakness that the bug comes to light only once the capital has already moved. The window between deployment and exploit is when risk runs highest, and defenses run thinnest.
TRM Labs’ 2026 Crypto Crime Report showed that illicit actors stole $2.87 billion across nearly 150 hacks and exploits in 2025. Infrastructure attacks via compromised keys, wallet infrastructure, privileged access, front-end surfaces, and control planes drove $2.2 billion of that total.
Code exploits, the category most audits directly address, accounted for $350 million, or 12.1%.
Hacken’s data for the first quarter reinforces that audit-centric security has real limits, since Web3 lost $482 million across 44 incidents in a single quarter. Six of those incidents involved audited protocols, including one that had received 18 separate audits.
A $282 million theft involved no code exploit, with the attacker bypassing the contract layer entirely and compromising the operational and social infrastructure around it.
CertiK’s most recent wrench-attack report noted that 34 verified physical coercion incidents occurred globally between January and April 2026, up 41% from the same period in 2025, with estimated losses of approximately $101 million over those four months.
At that trajectory, CertiK estimates 2026 could close with around 130 incidents. The attack vector is now the person holding the key, the signer in the multisig, and the engineer with cloud console access.
The three datasets together describe a threat that has migrated well above the smart contract.
What “resilient by design” requires in crypto
Daybreak’s logic, applied to crypto, points toward a security posture that runs continuously through the protocol lifecycle.
OpenAI describes AI that can reason across entire codebases, identify subtle vulnerabilities, validate that fixes actually resolve the underlying issue, and bring that capability into the everyday build-and-deploy workflow as an ongoing function.
For crypto, that translates into specific operational requirements across the full stack where losses are now concentrated.
AI-assisted secure code review running before and throughout deployment would catch logic errors, access-control gaps, and unsafe assumptions before they reach mainnet. Continuous threat modeling across protocol upgrades would assess how each architecture update, oracle dependency, bridge design, or governance mechanism opens new attack surfaces.
Dependency and oracle risk analysis would flag when a third-party integration weakens the security model of the protocol that relies on it.
Patch validation before governance execution would confirm that the proposed fixes close the vulnerability and that the fixes themselves hold under adversarial conditions.
Privileged-access review for multisigs, signers, front-end deployments, and custody systems would run on a regular cadence as part of standard operating procedures. Monitoring that catches abnormal behavior before funds leave would compress the time between detection and response.
| Security function | What it checks | Why it matters in crypto |
|---|---|---|
| AI-assisted secure code review | Contract logic, access controls, unsafe assumptions, upgrade-related bugs before and during deployment | Helps catch exploitable flaws before they reach mainnet, where failure can become immediate capital loss |
| Continuous threat modeling | How protocol upgrades, architecture changes, governance mechanics, oracle links, and bridge designs create new attack surfaces | Keeps security aligned with the protocol as it evolves, rather than treating risk as fixed at launch |
| Dependency and oracle risk analysis | Whether third-party libraries, oracle providers, middleware, or bridge components weaken the protocol’s security model | Many major failures now come from the wider stack around the contract, not the contract alone |
| Patch validation before governance execution | Whether a proposed fix actually closes the underlying vulnerability and remains safe under adversarial conditions | Prevents governance from approving patches that look correct but leave the exploit path open or create a new one |
| Privileged-access review | Multisigs, signers, custody systems, admin keys, cloud-console access, and front-end deployment permissions | Infrastructure attacks increasingly target the people and systems with authority to move funds or change protocol behavior |
| Monitoring before funds leave | Abnormal transaction patterns, suspicious signer behavior, unusual front-end changes, or withdrawal anomalies | Compresses the time between detection and response, giving teams a chance to intervene before losses escalate |
Crypto protocols with extensive audit records can still have unmonitored front-end deployments or misconfigured multisigs, leaving them in an operational blind spot where 2025’s largest losses occurred.
OpenAI said bad actors can misuse expanded cyber capability, and Daybreak pairs its defensive tooling with verification, scoped access, safeguards, misuse monitoring, and stronger account controls.
The same AI capabilities that help defenders review code, validate patches, and model threats can help attackers accelerate phishing, generate convincing fake front ends, clone legitimate protocols, analyze dependency chains for exploitable weaknesses, and scale social engineering across custodians, signers, and support channels.
Hacken’s data ranked phishing among the leading attack vectors, and CertiK’s data on physical coercion showed attackers targeting people directly. Both categories involve social and operational manipulation, and AI operates at scale in both.
Two outcomes for crypto security
The bull case is that “resilient by design” becomes a competitive standard.
Protocols begin treating continuous code review, signer-policy audits, dependency checks, front-end integrity monitoring, and governance-execution validation as standard requirements throughout the protocol lifecycle.
In that model, audit certification gives way to the full operational stack of signers, upgrades, dependencies, and access controls proving resilience before execution.
OpenAI’s own approach, coupling more capable tooling with stronger verification and process controls, is an external template for that direction.
According to TRM’s data, if 76% of losses come from infrastructure, that is where the next security standard needs to operate. Protocols that can demonstrate continuous operational resilience would have an easier time making their case with insurers, regulators, and institutional allocators than those that present only a stack of audit certifications.
The bear case is that AI-assisted security stays a marketing layer.
Protocols add AI-powered security language to their documentation, and the underlying operational model stays fixed in pre-launch audits and post-exploit post-mortems.
Attackers use the same tools to scale phishing, clone front ends faster, and compromise support channels more convincingly than defenders improve their workflows.
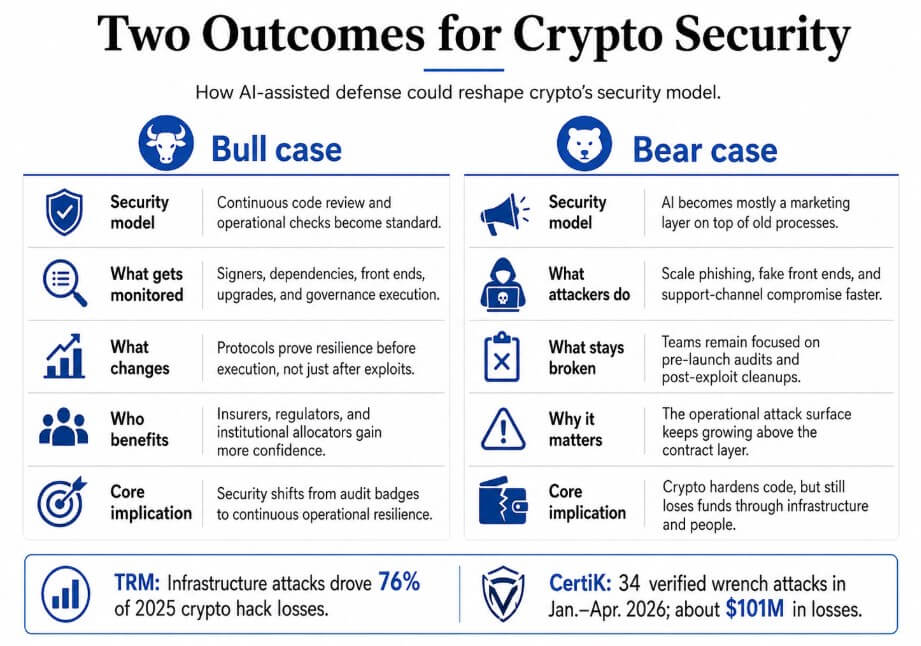
Hacken’s finding that one attacker stole $282 million without touching a single line of contract code shows that the attack surface extends beyond the contract layer, and the industry’s current security framework covers only a portion of it.
The crypto industry has focused its security model on post-exploit response and point-in-time review, and the attack surface has moved well beyond that frame.
The post OpenAI’s new cybersecurity push has a lesson for crypto: stop waiting for the hack appeared first on CryptoSlate.


