Bitcoin’s debate about quantum computers produced a published draft with real political consequences on Apr. 14.
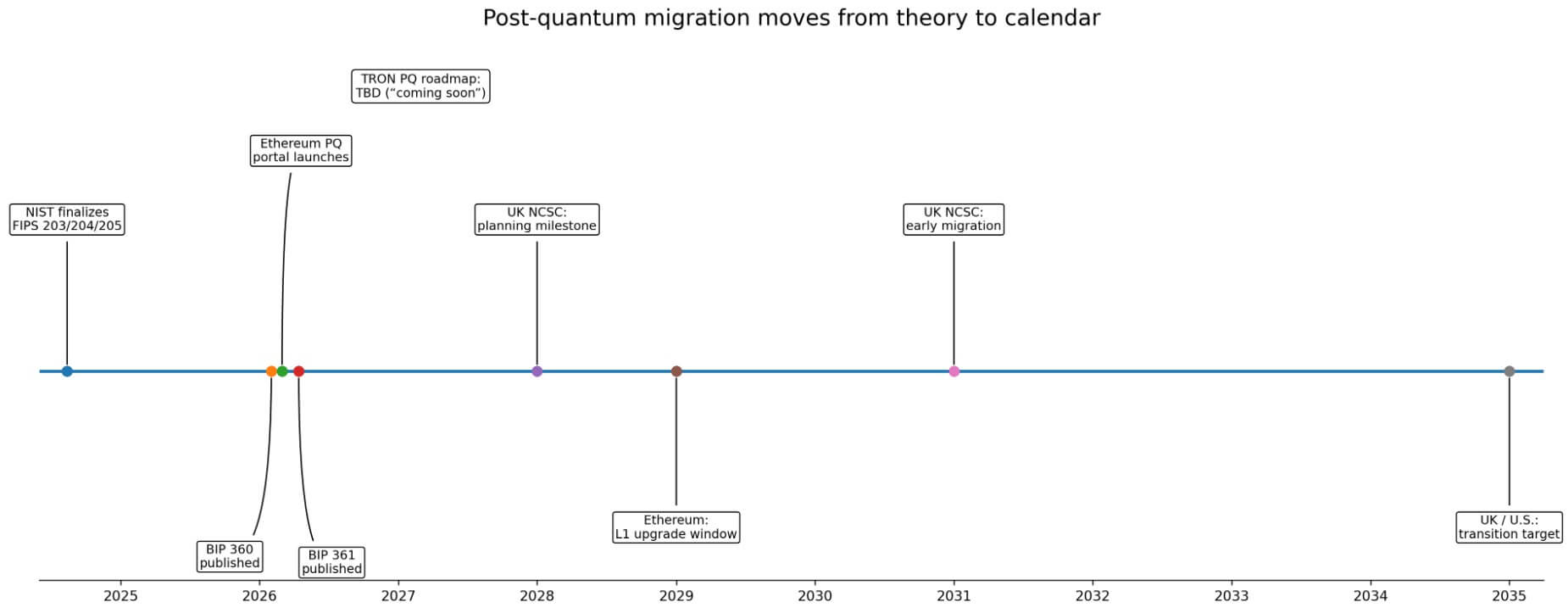
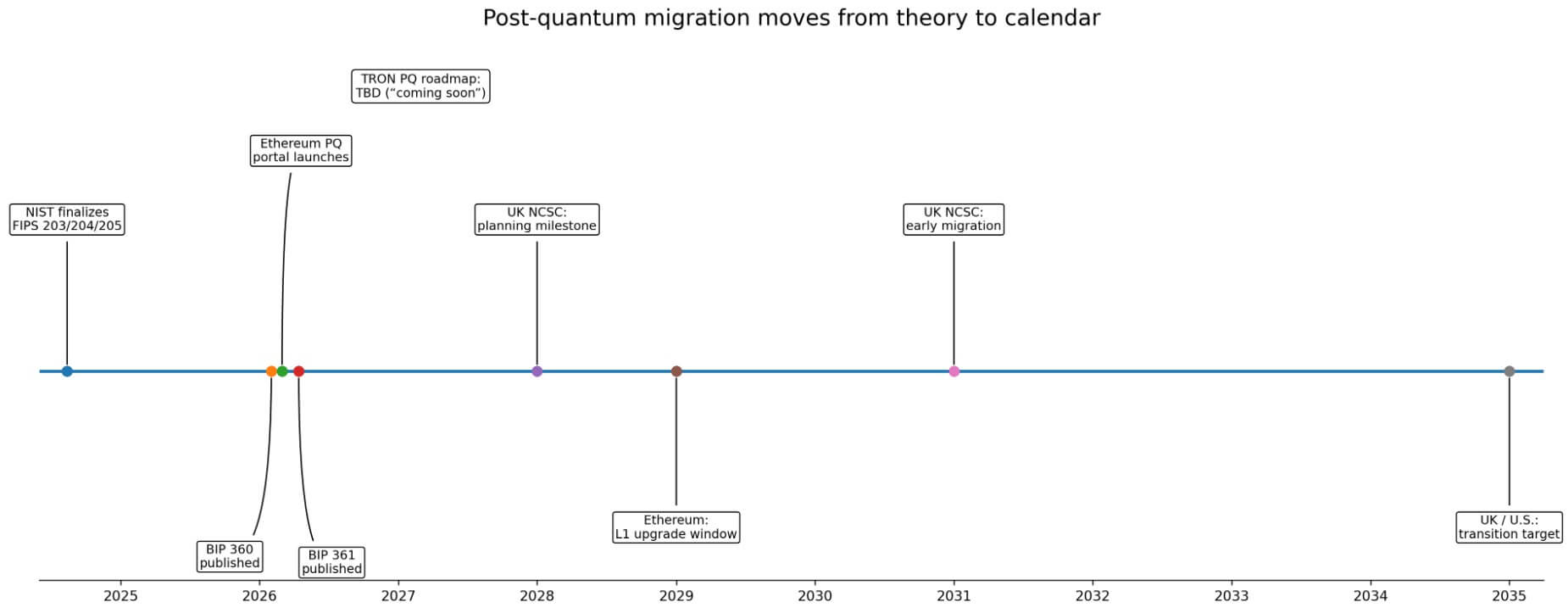
Bitcoin Improvement Proposal 361 (BIP 361), titled “Post Quantum Migration and Legacy Signature Sunset,” landed in Bitcoin’s official proposal repository with a three-phase plan to phase out ECDSA and Schnorr signature spends entirely once a quantum-resistant output type exists on the network.
The proposal builds directly on BIP 360, published in February, which introduced a new address format that strips Taproot’s quantum-vulnerable key-path spend, called Pay-to-Merkle-Root (P2MR). The proposal also preserved compatibility with Lightning, BitVM, and multi-signature setups.
Together, the two drafts constitute the most explicit governance posture Bitcoin has adopted regarding quantum migration to date.
What makes this moment sharp is the external calendar hardening around it, as NIST finalized FIPS 203, 204, and 205 in August 2024 and urged organizations to begin migrating immediately.
The UK’s NCSC has set migration milestones for 2028, 2031, and 2035, while US federal agencies face a 2035 quantum-transition target.
Governments, banks, and national cyber agencies already have migration deadlines on their calendars, making blockchains late arrivals to that debate.
Bitcoin’s coercive logic
What separates BIP 361 from prior Bitcoin post-quantum (PQ) discussions is its deliberate coerciveness.
Phase A, three years past the activation of a quantum-resistant address type, blocks new sends to vulnerable address formats. Phase B, two years later, invalidates ECDSA and Schnorr spends from quantum-vulnerable UTXOs at the consensus layer. Coins that have not migrated get frozen.
A possible Phase C would allow frozen coin holders to prove ownership via zero-knowledge proofs linked to a BIP-39 seed phrase and to recover their funds via a later recovery mechanism.
The proposal’s authors, including Jameson Lopp of Casa, frame this as a defense. As of Mar. 1, over 34% of all Bitcoin sat in addresses whose public keys had already been exposed on-chain, making those coins theoretically readable by a quantum machine running Shor’s algorithm.
Google researchers estimated in recent work that a sufficiently powerful quantum computer could crack a Bitcoin private key in roughly nine minutes, with one analysis citing 2029 as a plausible outer bound for a cryptographically relevant machine.
The counterargument arrived on the mailing list immediately.
Tadge Dryja, a Bitcoin developer and Lightning Network co-author, said that the plan is not viable in its current form because it ties the activation of quantum-resistant outputs to the deactivation of elliptic-curve outputs.
That link, Dryja argued, could destroy coins preemptively and relies on definitions of “quantum-vulnerable UTXO” still contested in practice.
The BIPs repository explicitly states that inclusion certifies only that a proposal met formal editorial criteria, with community endorsement and activation timing being separate determinations.
BIP 360 is already running on Bitcoin’s quantum testnet, deployed by BTQ Technologies in early 2026. BIP 361 co-author Ethan Heilman has estimated that a full Bitcoin migration to quantum resilience would take seven years from the day consensus forms.
Tron’s calculated entry
Justin Sun published his own declaration on post-quantum resistance.
In a post on X, the Tron founder announced that the network is officially launching a post-quantum upgrade initiative to become the first major public blockchain to deploy NIST-standardized post-quantum cryptographic signatures on mainnet.
Sun wrote that “while Bitcoin debates whether to freeze vulnerable coins and Ethereum forms research committees, Tron is building.” He added that a technical roadmap is “coming soon.”
Tron holds roughly $86.7 billion in stablecoins, about 97.78% of which is USDT, alongside approximately $5.1 billion in total value locked in DeFi.
Post-quantum readiness on a chain of that scale becomes a question of custody and settlement infrastructure. The networks, exchanges, and custodians moving dollar liquidity through Tron have operational keys, admin paths, and bridge mechanisms that a quantum attacker targeting high-value addresses would prioritize first.
Tron’s current public posture is narrative compression, consisting of decisive language and competitive positioning of the scheme selection, migration model, wallet compatibility plan, and activation path needed to verify what “first major public blockchain” actually means in practice.
| Category | Bitcoin | TRON | Ethereum |
|---|---|---|---|
| Governance style | Open, adversarial, consensus-driven | Executive-led, founder-driven messaging | Open, layered, research-led |
| Public status today | BIP 361 published as a draft in official repo; BIP 360 already published | Initiative announced by Justin Sun; roadmap still pending | Official PQ portal live; active roadmap and devnets |
| Core migration model | Phased sunset of legacy signatures after a PQ output exists | Undisclosed so far; Sun says NIST-standardized PQ signatures on mainnet | Gradual migration via account abstraction, precompiles, and later consensus changes |
| Main policy logic | Force migration with future restrictions and eventual invalidation of vulnerable spends | Claim speed and decisiveness before full technical detail | Build cryptographic agility and avoid a disruptive flag day |
| What users may face | New sends blocked to vulnerable formats, later frozen legacy coins if not migrated | Unknown until roadmap: optional, hybrid, or mandatory migration not yet specified | Wallet and account upgrades spread over time rather than a single cutoff |
| What is already specified publicly | Phase A / Phase B / possible Phase C; definition of vulnerable UTXOs under debate | Narrative claim, competitive framing, “roadmap coming soon” | Execution-, consensus-, and data-layer approach; weekly interoperability devnets |
| What is still missing | Consensus, activation path, final definition of quantum-vulnerable outputs | Scheme choice, migration model, wallet compatibility plan, activation path | Single fixed migration date or standalone flagship PQ proposal |
| Main risk/trade-off | Protect the network but risk freezing or stranding coins | Strong messaging without yet-published operational detail | Flexible migration but less coordination pressure on a fixed timetable |
| Key infrastructure at stake | Legacy UTXOs with exposed public keys | Stablecoin settlement rail, custody, admin keys, bridges | EOAs, bridges, validator keys, execution-layer migration |
| Best one-line summary | Certainty requires deadlines | Speed is the product | Safety requires agility |
NIST’s relevant standards, such as ML-DSA, FN-DSA, and SLH-DSA, carry different trade-offs in signature size, verification speed, and implementation complexity, and choosing among them is a material technical decision.
Ethereum’s layered bet
Ethereum takes the structural opposite of Bitcoin’s forced deadlines.
The Ethereum Foundation launched pq.ethereum.org in March 2026 as a hub for its post-quantum research, roadmap, and open-source repositories, with more than 10 client teams running weekly post-quantum interoperability devnets.
The roadmap spans three layers. At the execution layer, native account abstraction, as defined by EIP-7701 and EIP-8141, provides a built-in migration path away from ECDSA, allowing users to rotate to quantum-safe authentication via smart accounts without requiring a protocol-wide cutover.
At the consensus layer, BLS signatures would eventually give way to hash-based alternatives under the leanSig scheme, which combines XMSS-style quantum resistance with STARK-based aggregation to offset the size and performance costs of post-quantum primitives.
The Foundation’s own assessment places core L1 protocol upgrades around 2029, with full execution layer migration extending beyond that date.
Ethereum’s February 2026 protocol priorities post made the intersection explicit, with native account abstraction providing a natural migration path away from ECDSA-based authentication, while developers are working on complementary EIPs to make quantum-resistant signature verification cheaper in the EVM.
Ethereum has an official roadmap and an active engineering track, with Glamsterdam targeted for the first half of 2026, and it is arriving with no standalone quantum proposal introducing a fixed migration date.
Two futures for migration
The bull case runs through cryptographic agility.
If the threat stays far enough out, and NIST’s estimate that full integration can take 10 to 20 years from standardization supports that reading, chains can migrate without emergency powers.
Bitcoin’s sunset logic narrows to the most clearly exposed outputs or evolves into a softer incentive structure.
Tron eventually publishes a roadmap that names its scheme and migration model, and the market rewards systems that make migration boring: smart accounts, precompiles, key rotation, and wallet updates handled gradually enough that no user wakes up locked out.
Ethereum’s own team has said L1 protocol upgrades could be completed around 2029, the cleanest publicly stated timeline among the major chains in this race.
| Scenario | Bitcoin | TRON | Ethereum |
|---|---|---|---|
| Bull case: long runway, orderly migration | Sunset logic softens or narrows to the clearest exposed outputs; migration happens before emergency politics take over | TRON publishes a credible roadmap, names a scheme, and turns executive speed into operational execution | Account abstraction, precompiles, and staged upgrades make migration gradual and boring |
| What wins in this scenario | Clear incentives plus enough time for wallets and custodians to adapt | Fast coordination across wallets, exchanges, and stablecoin infrastructure | Cryptographic agility across layers without a disruptive flag day |
| Bear case: selective attacks arrive early | Pressure lands first on exposed or high-value legacy coins; governance fight over freezes happens before consensus is mature | Stablecoin rail concentration turns custody keys, admin paths, and bridges into prime targets | EOAs, bridges, and validator keys become the first pressure points |
| What breaks in this scenario | Political legitimacy of freezing coins vs letting them be stolen | Narrative advantage collapses if no published runbook exists | Diffuse roadmap looks slow if markets suddenly demand a hard timetable |
| Bottom line | Most direct defense, but also the most coercive | Fastest rhetoric, but proof depends on roadmap details | Most complete migration architecture, but still without a single forcing date |
The bear case begins where Ethereum’s own portal draws the boundary, and early quantum machines may target a small number of high-value keys.
Bitcoin faces its hardest political test under that scenario because BIP 361 already exposes more than 34% of BTC on-chain, and any selective attack on Satoshi-era or P2PK coins would force the governance question before consensus has formed.
Ethereum’s exposure is concentrated in externally owned accounts, bridges, and validator keys, the exact places a well-resourced attacker would try to exploit first.
Tron’s concentration as a USDT rail makes custody and admin-key migration the first thing to scrutinize, and a narrative initiative without a published technical roadmap offers no operational protection under those conditions.
Who decides
Bitcoin says certainty requires deadlines, Ethereum says safety requires agility, and Tron says speed is the product. None of those positions is obviously wrong.
A coercive Bitcoin deadline forces migration but risks leaving coins behind whose owners cannot be reached.
Ethereum’s layered approach spreads migration pain over years but lacks a single focal point to coordinate wallets, custodians, and exchanges on the same timetable.
Tron’s executive speed may prove real, or it may prove to be another well-timed announcement awaiting a second act.
The actual contest over which governance model can move users, infrastructure, and hundreds of billions in assets before a quantum adversary selects the weakest node belongs to whoever has a runbook when the window closes.


